Administrator Control of SELinux
In addition to the tasks often performed by users in "End User Control of SELinux", SELinux administrators could be expected to perform a number of additional tasks. These tasks typically require root access to the system. Such tasks are significantly easier under the targeted policy. For example, there is no need to consider adding, editing, or deleting Linux users from the SELinux users, nor do you need to consider roles.
This section covers the types of tasks required of an administrator who maintains Community Enterprise Linux running SELinux.
The The The You may never need to relabel an entire file system. This usually occurs only when labeling a file system for SELinux for the first time, or when switching between different types of policy, such as changing from the targeted to the strict policy.
Use the following procedure to relabel a file system using this method.
At boot time, Use the following command to relabel a file system only using the Use the following command to relabel a file system based on the RPM database:
Using Running If the relabeling operation applies a new policy that is different from the policy that was in place when the system booted, existing processes may be running in incorrect and insecure domains. For example, a process could be in a domain that is not an allowed transition for that process in the new policy, granting unexpected permissions to that process alone.
In addition, one of the options to In Community Enterprise Operating System, most targeted daemons do not interact with user data and are not affected by NFS-mounted home directories. One exception is the Apache HTTP Server. For example, CGI scripts that are on the mounted file system have the If you are having problems with the default type of "Specifying the Security Context of Entire File Systems" explains how to mount a directory so that Future versions of the SELinux policy address the functionality of NFS. Similar to standard Linux DAC permissions, a targeted daemon must have SELinux permissions to be able to descend the directory tree. This does not mean that a directory and its contents need to have the same type. There are many types, such as If you are working with an When trying to interpret AVC denial messages, do not be misled by the Refer to the explanation in "Creating Archives That Retain Security Contexts". You can enable and disable SELinux enforcement at runtime or configure it to start in the correct mode at boot time, using the command line or GUI. SELinux can operate in one of three modes: disabled, meaning not enabled in the kernel; permissive, meaning SELinux is running and logging but not controlling permissions; or enforcing, meaning SELinux is running and enforcing policy.
Use the The Note that changing the runtime enforcement does not affect the boot time configuration:
You can also disable enforcing mode for a single daemon. For example, if you are trying to troubleshoot the Use the Use the following command to disable enforcing mode for this daemon:
This sets the runtime value only. Use the Any *_disable_trans booleans that are set to "on" invoke the conditional that prevents the process from transitioning to the domain on execution.
Use the following command to find which of these booleans are set:
You can set any number of boolean values using the You can also use You can configure all of these settings using system-config-selinux. The same configuration files are used, so changes appear bidirectionally.
Administrator privileges are required to perform this procedure.
On the System menu, point to and then click Security Level and Firewall to display the Security Level Configuration dialog box. Click the SELinux tab, and then click Modify SELinux Policy.
In the selection list, click the arrow next to the Name Service entry, and select the Disable SELinux protection for named daemon check box.
Click OK to apply the change. Note that it may take a short time for the policy to be reloaded.
Using the Security Level Configuration dialog box to change a runtime boolean. If you want to control these settings with scripts, you can use the Changes you make to files while SELinux is disabled may give them an unexpected security label, and new files will not have a label. You may need to relabel part or all of the file system after re-enabling SELinux.
From the command line, you can edit the You need administrator privileges to perform this procedure.
On the System menu, point to and then click Security Level and Firewall to display the Security Level Configuration dialog box. Click the SELinux tab.
In the SELinux Setting select either If you changed from Changes made using this dialog box are immediately reflected in This section provides a brief introduction to using customized policies on your system. A full discussion of this topic is beyond the scope of this document.
To load a different policy on your system, change the following line in where Use the following procedure to load a different policy using the system-config-selinux utility:
You need administrator privileges to perform this procedure.
Ensure that the complete directory structure for the required policy exists under On the System menu, point to and then click Security Level and Firewall to display the Security Level Configuration dialog box.
Click the SELinux tab.
In the Policy Type list, select the policy that you want to load, and then click OK. This list is only visible if more than one policy is installed.
Restart the machine for the change to take effect.
Using the Security Level Configuration dialog box to load a custom policy. You can use the For example, if you need the Apache HTTP Server to read from a mounted directory or loopback file system, you need to set the type to When troubleshooting Refer to "Assigning Categories to Files" and "Assigning Categories to Users" for information about adding and changing the security categories of files and users. You can use the For example, you could use the following command to run a script to test for mislabeled content. The arguments that appear after the command are considered to be part of the command. (In this example, You can also specify the entire context, as follows:
The following is a list of useful commands introduced with SELinux, and which you may find useful when writing scripts to help administer your system:
This command returns the enforcing status of SELinux. This command controls the enforcing mode of SELinux. The option This command exits with a status of This command shows the status of all booleans ( This command sets one or more boolean values. The This command toggles the setting of one or more booleans. This effects boolean settings in memory only; changes are not persistent across reboots. You use the The The The primary reason for rebooting the system from an SELinux perspective is to completely relabel the file system. On occasion you might need to reboot the system to enable or disable SELinux.Viewing the Status of SELinux
sestatus command provides a configurable view into the status of SELinux. The simplest form of this command shows the following information:
~]#
sestatus
SELinux status: enabled
SELinuxfs mount: /selinux
Current mode: enforcing
Mode from config file: enforcing
Policy version: 21
Policy from config file: targeted-v option includes information about the security contexts of a series of files that are specified in /etc/sestatus.conf:
~]#
sestatus -v
SELinux status: enabled
SELinuxfs mount: /selinux
Current mode: enforcing
Mode from config file: enforcing
Policy version: 21
Policy from config file: targeted
Process contexts:
Current context: user_u:system_r:unconfined_t
Init context: system_u:system_r:init_t
/sbin/mingetty system_u:system_r:getty_t
/usr/sbin/sshd system_u:system_r:unconfined_t:s0-s0:c0.c1023
File contexts:
Controlling term: user_u:object_r:devpts_t
/etc/passwd system_u:object_r:etc_t
/etc/shadow system_u:object_r:shadow_t
/bin/bash system_u:object_r:shell_exec_t
/bin/login system_u:object_r:login_exec_t
/bin/sh system_u:object_r:bin_t -> system_u:object_r:shell_exec_t
/sbin/agetty system_u:object_r:getty_exec_t
/sbin/init system_u:object_r:init_exec_t
/sbin/mingetty system_u:object_r:getty_exec_t
/usr/sbin/sshd system_u:object_r:sshd_exec_t
/lib/libc.so.6 system_u:object_r:lib_t -> system_u:object_r:lib_t
/lib/ld-linux.so.2 system_u:object_r:lib_t -> system_u:object_r:ld_so_t-b displays the current state of booleans. You can use this in combination with grep or other tools to determine the status of particular booleans:
~]#
sestatus -b | grep httpd | grep on$
httpd_builtin_scripting on
httpd_disable_trans on
httpd_enable_cgi on
httpd_enable_homedirs on
httpd_unified onRelabeling a File System
Relabeling a File System Using init
The recommended method for relabeling a file system is to reboot the machine. This allows the init process to perform the relabeling, ensuring that applications have the correct labels when they are started and that they are started in the right order. If you relabel a file system without rebooting, some processes may continue running with an incorrect context. Manually ensuring that all the daemons are restarted and running in the correct context can be difficult.
touch /.autorelabel
rebootinit.rc checks for the existence of /.autorelabel. If this file exists, SELinux performs a complete file system relabel (using the /sbin/fixfiles -f -F relabel command), and then deletes /.autorelabel.
Relabeling a File System Using fixfiles
It is possible to relabel a file system using the fixfiles command, or to relabel based on the RPM database:
fixfiles command:
fixfiles relabelfixfiles -R <packagename> restorefixfiles to restore contexts from packages is safer and quicker.
fixfiles on the entire file system without rebooting may make the system unstable.
fixfiles relabel prompts for approval to empty /tmp/ because it is not possible to reliably relabel /tmp/. Since fixfiles is run as root, temporary files that applications are relying upon are erased. This could make the system unstable or behave unexpectedly.
Managing NFS Home Directories
nfs_t type, which is not a type that httpd_t is allowed to execute.
nfs_t, try mounting the home directories with a different context:
mount -t nfs -o context=user_u:object_r:user_home_dir_t \
fileserver.example.com:/shared/homes/ /homehttpd can execute scripts. If you do this for user home directories, it gives the Apache HTTP Server increased access to those directories. Remember that a mountpoint label applies to the entire mounted file system.
Granting Access to a Directory or a Tree
root_t, tmp_t, and usr_t that grant read access for a directory. These types are suitable for directories that do not contain any confidential information, and that you want to be widely readable. They could also be used for a parent directory of more secured directories with different contexts.
avc: denied message, there are some common problems that arise with directory traversal. For example, many programs run a command equivalent to ls -l / that is not necessary to their operation but generates a denial message in the logs. For this you need to create a dontaudit rule in your local.te file.
path=/ component. This path is not related to the label for the root file system, /. It is actually relative to the root of the file system on the device node. For example, if your /var/ directory is located on an LVM (Logical Volume Management [22]) device, /dev/dm-0, the device node is identified in the message as dev=dm-0. When you see path=/ in this example, that is the top level of the LVM device dm-0, not necessarily the same as the root file system designation /.Backing Up and Restoring the System
Enabling or Disabling Enforcement
setenforce command to change between permissive and enforcing modes at runtime. Use setenforce 0 to enter permissive mode; use setenforce 1 to enter enforcing mode.
sestatus command displays the current mode and the mode from the configuration file referenced during boot:
~]#
sestatus | grep -i mode
Current mode: permissive
Mode from config file: permissive~]#
setenforce 1
~]# sestatus | grep -i mode
Current mode: enforcing
Mode from config file: permissivenamed daemon and SELinux, you can turn off enforcing for just that daemon.
getsebool command to get the current status of the boolean:
~]#
getsebool named_disable_trans
named_disable_trans --> off~]#
setsebool named_disable_trans 1
~]# getsebool named_disable_trans
named_disable_trans --> on-P option to make the change persistent across reboots.
~]#
getsebool -a | grep disable.*on
httpd_disable_trans=1
mysqld_disable_trans=1
ntpd_disable_trans=1setsebool command:
setsebool -P httpd_disable_trans=1 mysqld_disable_trans=1 ntpd_disable_trans=1togglesebool to change the value of a specific boolean:
<boolean_name>~]#
getsebool httpd_disable_trans
httpd_disable_trans --> off
~]# togglesebool httpd_disable_trans
httpd_disable_trans: activeChanging a Runtime Boolean
Use the following procedure to change a runtime boolean using the GUI.
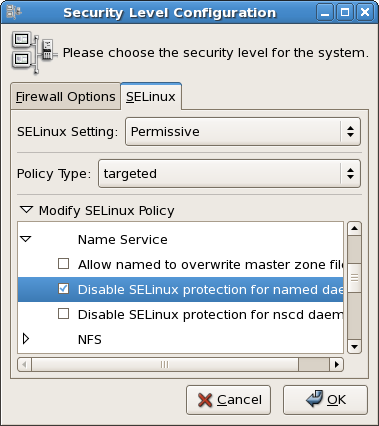
Figure 48.1. Using the Security Level Configuration dialog box to change a runtime boolean.
setenforce(1), getenforce(1), and selinuxenabled(1) commands.Enable or Disable SELinux
/etc/sysconfig/selinux file. This file is a symlink to /etc/selinux/config. The configuration file is self-explanatory. Changing the value of SELINUX or SELINUXTYPE changes the state of SELinux and the name of the policy to be used the next time the system boots.
~]#
cat /etc/sysconfig/selinux
# This file controls the state of SELinux on the system.
# SELINUX= can take one of these three values:
# enforcing - SELinux security policy is enforced.
# permissive - SELinux prints warnings instead of enforcing.
# disabled - SELinux is fully disabled.
SELINUX=permissive
# SELINUXTYPE= type of policy in use. Possible values are:
# targeted - Only targeted network daemons are protected.
# strict - Full SELinux protection.
SELINUXTYPE=targeted
# SETLOCALDEFS= Check local definition changes
SETLOCALDEFS=0Changing the Mode of SELinux Using the GUI
Use the following procedure to change the mode of SELinux using the GUI.
Disabled, Enforcing or Permissive, and then click OK.
Enabled to Disabled or vice versa, you need to restart the machine for the change to take effect.
/etc/sysconfig/selinux.Changing the Policy
/etc/sysconfig/selinux:
SELINUXTYPE=
<policyname><policyname> is the policy name directory under /etc/selinux/. This assumes that you have the custom policy installed. After changing the SELINUXTYPE parameter, run the following commands:
touch /.autorelabel
reboot
/etc/selinux.
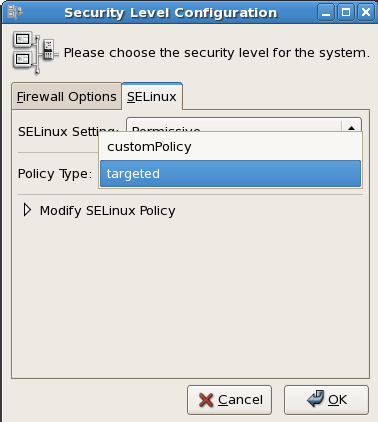
Figure 48.2. Using the Security Level Configuration dialog box to load a custom policy.
Specifying the Security Context of Entire File Systems
mount -o context= command to set a single context for an entire file system. This might be a file system that is already mounted and that supports xattrs, or a network file system that obtains a genfs label such as cifs_t or nfs_t.
httpd_sys_content_t:
mount -t nfs -o context=system_u:object_r:httpd_sys_content_t \
server1.example.com:/shared/scripts /var/www/cgihttpd and SELinux problems, reduce the complexity of your situation. For example, if you have the file system mounted at /mnt and then symbolically linked to /var/www/html/foo, you have two security contexts to be concerned with. Because one security context is of the object class file and the other of type lnk_file, they are treated differently by the policy and unexpected behavior may occur.Changing the Security Category of a File or User
Running a Command in a Specific Security Context
runcon command to run a command in a specific context. This is useful for scripting or for testing policy, but care should be taken to ensure that it is implemented correctly.
~/bin/contexttest is a user-defined script.)
runcon -t httpd_t ~/bin/contexttest -ARG1 -ARG2runcon user_u:system_r:httpd_t ~/bin/contexttestUseful Commands for Scripts
getenforce
setenforce [
Enforcing | Permissive | 1 | 0 ]1 or Enforcing tells SELinux to enter enforcing mode. The option 0 or Permissive tells SELinux to enter passive mode. Access violations are still logged, but not prevented.
selinuxenabled
0 if SELinux is enabled, and 1 if SELinux is disabled.
~]#
selinuxenabled
~]# echo $?
0getsebool [-a] [
boolean_name]-a) or a specific boolean (<boolean_name>).
setsebool [-P] <boolean_name> value | bool1=val1 bool2=val2 ...
-P option makes the changes persistent across reboots.
togglesebool boolean ...
Changing to a Different Role
newrole command to run a new shell with the specified type and/or role. Changing roles is typically only meaningful in the strict policy; the targeted policy is generally restricted to a single role. Changing types may be useful for testing, validation, and development purposes.
newrole -r <role_r> -t <type_t> [-- [ARGS]...]ARGS are passed directly to the shell specified in the user's entry in the /etc/passwd file.
newrole command is part of the policycoreutils-newrole package, which is required if you install the strict or MLS policy. It is not installed by default in Community Enterprise Linux.When to Reboot